- Tunnelblick Not Connecting To My
- Tunnelblick Not Connecting Video
- Tunnelblick Connected But Not Working
- Tunnelblick Not Connecting Big Sur
- Tunnelblick Not Connecting To Internet
Tunnelblick Not Connecting To My
Hello,- If you have a Unity account already, you can sign in here and skip the rest of this guide. If you do not have a Unity account, click “create one”. Fill in the forms to create your Unity account. Then click “Create a Unity ID”. Alternatively, you have the option of signing up with a Google or Facebook account.
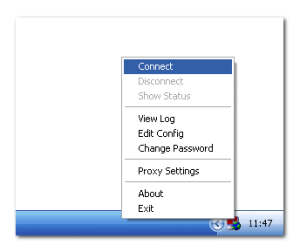
- In addition, on the 'Preferences' tab, make sure that 'Check if the apparent public IP address changed after connection' is checked. That can help diagnose problems with the VPN. You should have one of two results: either Tunnelblick will say that DNS is not working, or Tunnelblick will say that the Internet is not.
Hi, thanks for responding. I have connection inconsistencies using Tunnelblick with my home wifi network. I don’t use Tunnelblick with the wifi hotspot on the dappnode. For that, I just connect directly, with no problems. Tunnelblick VPN Issue: Public Address Not Different After Connecting.
I was able to set up a working OpenVPN server on a Debian server using Digital Ocean's guide for setting up OpenVPN on Ubuntu.
The server has two network interfaces, each within a different subnet (i.e. 10.10.128.0/24 and 192.168.24.0/24 ). I do not have a true DMZ in the network, but the 10.10.128.0/24 zone is where I am placing servers accessible to the outside, while the 192.168.24.0./24 is my truly private network with my personal computer etc., sitting behind another router.
The OpenVPN server is thus providing access for outside clients to access the 192.168.24.0/24 subnet (via routing), for remote desktop and other purposes.
Any computer in my network can successfully connect to the VPN server at 10.10.128.16 (incoming connection from another 10.10.128.0/24 IP address), but any connection attempt from the internet (e.g. incoming IP 172.56.x.x) fails. I do not see any firewall blocking or other error messages; it simply appears that the OpenVPN server is 'not responding' to the incoming requests.
So much for the background, so on to the configuration and log details I have gone through without finding the problem.
I'm running Debian Jessie:Here's my network configuration
Code: Select all
This is my server.conf: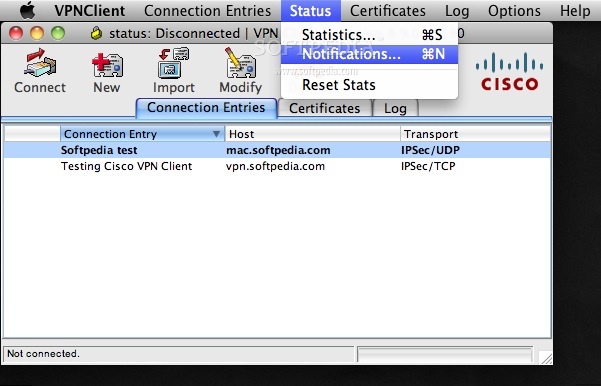
#################################################
# Sample OpenVPN 2.0 config file for #
# multi-client server. #
# #
# This file is for the server side #
# of a many-clients <-> one-server #
# OpenVPN configuration. #
# #
# OpenVPN also supports #
# single-machine <-> single-machine #
# configurations (See the Examples page #
# on the web site for more info). #
# #
# This config should work on Windows #
# or Linux/BSD systems. Remember on #
# Windows to quote pathnames and use #
# double backslashes, e.g.: #
# 'C:Program FilesOpenVPNconfigfoo.key' #
# #
# Comments are preceded with '#' or ';' #
#################################################
# Which local IP address should OpenVPN
# listen on? (optional)
;local a.b.c.d
# Which TCP/UDP port should OpenVPN listen on?
# If you want to run multiple OpenVPN instances
# on the same machine, use a different port
# number for each one. You will need to
# open up this port on your firewall.
port 6354
# TCP or UDP server?
;proto tcp
proto udp
# 'dev tun' will create a routed IP tunnel,
# 'dev tap' will create an ethernet tunnel.
# Use 'dev tap0' if you are ethernet bridging
# and have precreated a tap0 virtual interface
# and bridged it with your ethernet interface.
# If you want to control access policies
# over the VPN, you must create firewall
# rules for the the TUN/TAP interface.
# On non-Windows systems, you can give
# an explicit unit number, such as tun0.
# On Windows, use 'dev-node' for this.
# On most systems, the VPN will not function
# unless you partially or fully disable
# the firewall for the TUN/TAP interface.
;dev tap
dev tun
# Windows needs the TAP-Win32 adapter name
# from the Network Connections panel if you
# have more than one. On XP SP2 or higher,
# you may need to selectively disable the
# Windows firewall for the TAP adapter.
# Non-Windows systems usually don't need this.
;dev-node MyTap
# SSL/TLS root certificate (ca), certificate
# (cert), and private key (key). Each client
# and the server must have their own cert and
# key file. The server and all clients will
# use the same ca file.
#
# See the 'easy-rsa' directory for a series
# of scripts for generating RSA certificates
# and private keys. Remember to use
# a unique Common Name for the server
# and each of the client certificates.
#
# Any X509 key management system can be used.
# OpenVPN can also use a PKCS #12 formatted key file
# (see 'pkcs12' directive in man page).
ca ca.crt
cert server.crt
key server.key # This file should be kept secret
# Diffie hellman parameters.
# Generate your own with:
# openssl dhparam -out dh1024.pem 1024
# Substitute 2048 for 1024 if you are using
# 2048 bit keys.
dh dh2048.pem
# Configure server mode and supply a VPN subnet
# for OpenVPN to draw client addresses from.
# The server will take 10.8.0.1 for itself,
# the rest will be made available to clients.
# Each client will be able to reach the server
# on 10.8.0.1. Comment this line out if you are
# ethernet bridging. See the man page for more info.
server 10.8.0.0 255.255.255.0
# Maintain a record of client <-> virtual IP address
# associations in this file. If OpenVPN goes down or
# is restarted, reconnecting clients can be assigned
# the same virtual IP address from the pool that was
# previously assigned.
ifconfig-pool-persist ipp.txt
# Configure server mode for ethernet bridging.
# You must first use your OS's bridging capability
# to bridge the TAP interface with the ethernet
# NIC interface. Then you must manually set the
# IP/netmask on the bridge interface, here we
# assume 10.8.0.4/255.255.255.0. Finally we
# must set aside an IP range in this subnet
# (start=10.8.0.50 end=10.8.0.100) to allocate
# to connecting clients. Leave this line commented
# out unless you are ethernet bridging.
;server-bridge 10.8.0.4 255.255.255.0 10.8.0.50 10.8.0.100
# Configure server mode for ethernet bridging
# using a DHCP-proxy, where clients talk
# to the OpenVPN server-side DHCP server
# to receive their IP address allocation
# and DNS server addresses. You must first use
# your OS's bridging capability to bridge the TAP
# interface with the ethernet NIC interface.
# Note: this mode only works on clients (such as
# Windows), where the client-side TAP adapter is
# bound to a DHCP client.
;server-bridge
# Push routes to the client to allow it
# to reach other private subnets behind
# the server. Remember that these
# private subnets will also need
# to know to route the OpenVPN client
# address pool (10.8.0.0/255.255.255.0)
# back to the OpenVPN server.
;push 'route 192.168.10.0 255.255.255.0'
;push 'route 192.168.20.0 255.255.255.0'
# To assign specific IP addresses to specific
# clients or if a connecting client has a private
# subnet behind it that should also have VPN access,
# use the subdirectory 'ccd' for client-specific
# configuration files (see man page for more info).
# EXAMPLE: Suppose the client
# having the certificate common name 'Thelonious'
# also has a small subnet behind his connecting
# machine, such as 192.168.40.128/255.255.255.248.
# First, uncomment out these lines:
;client-config-dir ccd
;route 192.168.40.128 255.255.255.248
# Then create a file ccd/Thelonious with this line:
# iroute 192.168.40.128 255.255.255.248
# This will allow Thelonious' private subnet to
# access the VPN. This example will only work
# if you are routing, not bridging, i.e. you are
# using 'dev tun' and 'server' directives.
# EXAMPLE: Suppose you want to give
# Thelonious a fixed VPN IP address of 10.9.0.1.
# First uncomment out these lines:
;client-config-dir ccd
;route 10.9.0.0 255.255.255.252
# Then add this line to ccd/Thelonious:
# ifconfig-push 10.9.0.1 10.9.0.2
# Suppose that you want to enable different
# firewall access policies for different groups
# of clients. There are two methods:
# (1) Run multiple OpenVPN daemons, one for each
# group, and firewall the TUN/TAP interface
# for each group/daemon appropriately.
# (2) (Advanced) Create a script to dynamically
# modify the firewall in response to access
# from different clients. See man
# page for more info on learn-address script.
;learn-address ./script
# If enabled, this directive will configure
# all clients to redirect their default
# network gateway through the VPN, causing
# all IP traffic such as web browsing and
# and DNS lookups to go through the VPN
# (The OpenVPN server machine may need to NAT
# or bridge the TUN/TAP interface to the internet
# in order for this to work properly).
push 'redirect-gateway def1 bypass-dhcp'
# Certain Windows-specific network settings
# can be pushed to clients, such as DNS
# or WINS server addresses. CAVEAT:
# http://openvpn.net/faq.html#dhcpcaveats
# The addresses below refer to the public
# DNS servers provided by opendns.com.
push 'dhcp-option DNS 192.168.24.1'
push 'dhcp-option DNS 77.109.148.137'
# Uncomment this directive to allow different
# clients to be able to 'see' each other.
# By default, clients will only see the server.
# To force clients to only see the server, you
# will also need to appropriately firewall the
# server's TUN/TAP interface.
;client-to-client
# Uncomment this directive if multiple clients
# might connect with the same certificate/key
# files or common names. This is recommended
# only for testing purposes. For production use,
# each client should have its own certificate/key
# pair.
#
# IF YOU HAVE NOT GENERATED INDIVIDUAL
# CERTIFICATE/KEY PAIRS FOR EACH CLIENT,
# EACH HAVING ITS OWN UNIQUE 'COMMON NAME',
# UNCOMMENT THIS LINE OUT.
;duplicate-cn
# The keepalive directive causes ping-like
# messages to be sent back and forth over
# the link so that each side knows when
# the other side has gone down.
# Ping every 10 seconds, assume that remote
# peer is down if no ping received during
# a 120 second time period.
keepalive 10 120
# For extra security beyond that provided
# by SSL/TLS, create an 'HMAC firewall'
# to help block DoS attacks and UDP port flooding.
#
# Generate with:
# openvpn --genkey --secret ta.key
#
# The server and each client must have
# a copy of this key.
# The second parameter should be '0'
# on the server and '1' on the clients.
tls-auth ta.key 0 # This file is secret
key-direction 0
# Select a cryptographic cipher.
# This config item must be copied to
# the client config file as well.
;cipher BF-CBC # Blowfish (default)
cipher AES-128-CBC # AES
auth SHA256
;cipher DES-EDE3-CBC # Triple-DES
# Enable compression on the VPN link.
# If you enable it here, you must also
# enable it in the client config file.
comp-lzo
# The maximum number of concurrently connected
# clients we want to allow.
;max-clients 100
# It's a good idea to reduce the OpenVPN
# daemon's privileges after initialization.
#
# You can uncomment this out on
# non-Windows systems.
user nobody
group nogroup
# The persist options will try to avoid
# accessing certain resources on restart
# that may no longer be accessible because
# of the privilege downgrade.
persist-key
persist-tun
# Output a short status file showing
# current connections, truncated
# and rewritten every minute.
status openvpn-status.log
# By default, log messages will go to the syslog (or
# on Windows, if running as a service, they will go to
# the 'Program FilesOpenVPNlog' directory).
# Use log or log-append to override this default.
# 'log' will truncate the log file on OpenVPN startup,
# while 'log-append' will append to it. Use one
# or the other (but not both).
;log openvpn.log
;log-append openvpn.log
# Set the appropriate level of log
# file verbosity.
#
# 0 is silent, except for fatal errors
# 4 is reasonable for general usage
# 5 and 6 can help to debug connection problems
# 9 is extremely verbose
verb 3
# Silence repeating messages. At most 20
# sequential messages of the same message
# category will be output to the log.
;mute 20
And here's the client configuration for LAN testing (of course with certificates and keys removed):# Sample OpenVPN 2.0 config file for #
# multi-client server. #
# #
# This file is for the server side #
# of a many-clients <-> one-server #
# OpenVPN configuration. #
# #
# OpenVPN also supports #
# single-machine <-> single-machine #
# configurations (See the Examples page #
# on the web site for more info). #
# #
# This config should work on Windows #
# or Linux/BSD systems. Remember on #
# Windows to quote pathnames and use #
# double backslashes, e.g.: #
# 'C:Program FilesOpenVPNconfigfoo.key' #
# #
# Comments are preceded with '#' or ';' #
#################################################
# Which local IP address should OpenVPN
# listen on? (optional)
;local a.b.c.d
# Which TCP/UDP port should OpenVPN listen on?
# If you want to run multiple OpenVPN instances
# on the same machine, use a different port
# number for each one. You will need to
# open up this port on your firewall.
port 6354
# TCP or UDP server?
;proto tcp
proto udp
# 'dev tun' will create a routed IP tunnel,
# 'dev tap' will create an ethernet tunnel.
# Use 'dev tap0' if you are ethernet bridging
# and have precreated a tap0 virtual interface
# and bridged it with your ethernet interface.
# If you want to control access policies
# over the VPN, you must create firewall
# rules for the the TUN/TAP interface.
# On non-Windows systems, you can give
# an explicit unit number, such as tun0.
# On Windows, use 'dev-node' for this.
# On most systems, the VPN will not function
# unless you partially or fully disable
# the firewall for the TUN/TAP interface.
;dev tap
dev tun
# Windows needs the TAP-Win32 adapter name
# from the Network Connections panel if you
# have more than one. On XP SP2 or higher,
# you may need to selectively disable the
# Windows firewall for the TAP adapter.
# Non-Windows systems usually don't need this.
;dev-node MyTap
# SSL/TLS root certificate (ca), certificate
# (cert), and private key (key). Each client
# and the server must have their own cert and
# key file. The server and all clients will
# use the same ca file.
#
# See the 'easy-rsa' directory for a series
# of scripts for generating RSA certificates
# and private keys. Remember to use
# a unique Common Name for the server
# and each of the client certificates.
#
# Any X509 key management system can be used.
# OpenVPN can also use a PKCS #12 formatted key file
# (see 'pkcs12' directive in man page).
ca ca.crt
cert server.crt
key server.key # This file should be kept secret
# Diffie hellman parameters.
# Generate your own with:
# openssl dhparam -out dh1024.pem 1024
# Substitute 2048 for 1024 if you are using
# 2048 bit keys.
dh dh2048.pem
# Configure server mode and supply a VPN subnet
# for OpenVPN to draw client addresses from.
# The server will take 10.8.0.1 for itself,
# the rest will be made available to clients.
# Each client will be able to reach the server
# on 10.8.0.1. Comment this line out if you are
# ethernet bridging. See the man page for more info.
server 10.8.0.0 255.255.255.0
# Maintain a record of client <-> virtual IP address
# associations in this file. If OpenVPN goes down or
# is restarted, reconnecting clients can be assigned
# the same virtual IP address from the pool that was
# previously assigned.
ifconfig-pool-persist ipp.txt
# Configure server mode for ethernet bridging.
# You must first use your OS's bridging capability
# to bridge the TAP interface with the ethernet
# NIC interface. Then you must manually set the
# IP/netmask on the bridge interface, here we
# assume 10.8.0.4/255.255.255.0. Finally we
# must set aside an IP range in this subnet
# (start=10.8.0.50 end=10.8.0.100) to allocate
# to connecting clients. Leave this line commented
# out unless you are ethernet bridging.
;server-bridge 10.8.0.4 255.255.255.0 10.8.0.50 10.8.0.100
# Configure server mode for ethernet bridging
# using a DHCP-proxy, where clients talk
# to the OpenVPN server-side DHCP server
# to receive their IP address allocation
# and DNS server addresses. You must first use
# your OS's bridging capability to bridge the TAP
# interface with the ethernet NIC interface.
# Note: this mode only works on clients (such as
# Windows), where the client-side TAP adapter is
# bound to a DHCP client.
;server-bridge
# Push routes to the client to allow it
# to reach other private subnets behind
# the server. Remember that these
# private subnets will also need
# to know to route the OpenVPN client
# address pool (10.8.0.0/255.255.255.0)
# back to the OpenVPN server.
;push 'route 192.168.10.0 255.255.255.0'
;push 'route 192.168.20.0 255.255.255.0'
# To assign specific IP addresses to specific
# clients or if a connecting client has a private
# subnet behind it that should also have VPN access,
# use the subdirectory 'ccd' for client-specific
# configuration files (see man page for more info).
# EXAMPLE: Suppose the client
# having the certificate common name 'Thelonious'
# also has a small subnet behind his connecting
# machine, such as 192.168.40.128/255.255.255.248.
# First, uncomment out these lines:
;client-config-dir ccd
;route 192.168.40.128 255.255.255.248
# Then create a file ccd/Thelonious with this line:
# iroute 192.168.40.128 255.255.255.248
# This will allow Thelonious' private subnet to
# access the VPN. This example will only work
# if you are routing, not bridging, i.e. you are
# using 'dev tun' and 'server' directives.
# EXAMPLE: Suppose you want to give
# Thelonious a fixed VPN IP address of 10.9.0.1.
# First uncomment out these lines:
;client-config-dir ccd
;route 10.9.0.0 255.255.255.252
# Then add this line to ccd/Thelonious:
# ifconfig-push 10.9.0.1 10.9.0.2
# Suppose that you want to enable different
# firewall access policies for different groups
# of clients. There are two methods:
# (1) Run multiple OpenVPN daemons, one for each
# group, and firewall the TUN/TAP interface
# for each group/daemon appropriately.
# (2) (Advanced) Create a script to dynamically
# modify the firewall in response to access
# from different clients. See man
# page for more info on learn-address script.
;learn-address ./script
# If enabled, this directive will configure
# all clients to redirect their default
# network gateway through the VPN, causing
# all IP traffic such as web browsing and
# and DNS lookups to go through the VPN
# (The OpenVPN server machine may need to NAT
# or bridge the TUN/TAP interface to the internet
# in order for this to work properly).
push 'redirect-gateway def1 bypass-dhcp'
# Certain Windows-specific network settings
# can be pushed to clients, such as DNS
# or WINS server addresses. CAVEAT:
# http://openvpn.net/faq.html#dhcpcaveats
# The addresses below refer to the public
# DNS servers provided by opendns.com.
push 'dhcp-option DNS 192.168.24.1'
push 'dhcp-option DNS 77.109.148.137'
# Uncomment this directive to allow different
# clients to be able to 'see' each other.
# By default, clients will only see the server.
# To force clients to only see the server, you
# will also need to appropriately firewall the
# server's TUN/TAP interface.
;client-to-client
# Uncomment this directive if multiple clients
# might connect with the same certificate/key
# files or common names. This is recommended
# only for testing purposes. For production use,
# each client should have its own certificate/key
# pair.
#
# IF YOU HAVE NOT GENERATED INDIVIDUAL
# CERTIFICATE/KEY PAIRS FOR EACH CLIENT,
# EACH HAVING ITS OWN UNIQUE 'COMMON NAME',
# UNCOMMENT THIS LINE OUT.
;duplicate-cn
# The keepalive directive causes ping-like
# messages to be sent back and forth over
# the link so that each side knows when
# the other side has gone down.
# Ping every 10 seconds, assume that remote
# peer is down if no ping received during
# a 120 second time period.
keepalive 10 120
# For extra security beyond that provided
# by SSL/TLS, create an 'HMAC firewall'
# to help block DoS attacks and UDP port flooding.
#
# Generate with:
# openvpn --genkey --secret ta.key
#
# The server and each client must have
# a copy of this key.
# The second parameter should be '0'
# on the server and '1' on the clients.
tls-auth ta.key 0 # This file is secret
key-direction 0
# Select a cryptographic cipher.
# This config item must be copied to
# the client config file as well.
;cipher BF-CBC # Blowfish (default)
cipher AES-128-CBC # AES
auth SHA256
;cipher DES-EDE3-CBC # Triple-DES
# Enable compression on the VPN link.
# If you enable it here, you must also
# enable it in the client config file.
comp-lzo
# The maximum number of concurrently connected
# clients we want to allow.
;max-clients 100
# It's a good idea to reduce the OpenVPN
# daemon's privileges after initialization.
#
# You can uncomment this out on
# non-Windows systems.
user nobody
group nogroup
# The persist options will try to avoid
# accessing certain resources on restart
# that may no longer be accessible because
# of the privilege downgrade.
persist-key
persist-tun
# Output a short status file showing
# current connections, truncated
# and rewritten every minute.
status openvpn-status.log
# By default, log messages will go to the syslog (or
# on Windows, if running as a service, they will go to
# the 'Program FilesOpenVPNlog' directory).
# Use log or log-append to override this default.
# 'log' will truncate the log file on OpenVPN startup,
# while 'log-append' will append to it. Use one
# or the other (but not both).
;log openvpn.log
;log-append openvpn.log
# Set the appropriate level of log
# file verbosity.
#
# 0 is silent, except for fatal errors
# 4 is reasonable for general usage
# 5 and 6 can help to debug connection problems
# 9 is extremely verbose
verb 3
# Silence repeating messages. At most 20
# sequential messages of the same message
# category will be output to the log.
;mute 20
##############################################
# Sample client-side OpenVPN 2.0 config file #
# for connecting to multi-client server. #
# #
# This configuration can be used by multiple #
# clients, however each client should have #
# its own cert and key files. #
# #
# On Windows, you might want to rename this #
# file so it has a .ovpn extension #
##############################################
# Specify that we are a client and that we
# will be pulling certain config file directives
# from the server.
client
# Use the same setting as you are using on
# the server.
# On most systems, the VPN will not function
# unless you partially or fully disable
# the firewall for the TUN/TAP interface.
;dev tap
dev tun
# Windows needs the TAP-Win32 adapter name
# from the Network Connections panel
# if you have more than one. On XP SP2,
# you may need to disable the firewall
# for the TAP adapter.
;dev-node MyTap
# Are we connecting to a TCP or
# UDP server? Use the same setting as
# on the server.
;proto tcp
proto udp
# The hostname/IP and port of the server.
# You can have multiple remote entries
# to load balance between the servers.
remote 10.10.128.16 6354
# Choose a random host from the remote
# list for load-balancing. Otherwise
# try hosts in the order specified.
;remote-random
# Keep trying indefinitely to resolve the
# host name of the OpenVPN server. Very useful
# on machines which are not permanently connected
# to the internet such as laptops.
resolv-retry infinite
# Most clients don't need to bind to
# a specific local port number.
nobind
# Downgrade privileges after initialization (non-Windows only)
user nobody
group nogroup
# Try to preserve some state across restarts.
persist-key
persist-tun
# If you are connecting through an
# HTTP proxy to reach the actual OpenVPN
# server, put the proxy server/IP and
# port number here. See the man page
# if your proxy server requires
# authentication.
;http-proxy-retry # retry on connection failures
;http-proxy [proxy server] [proxy port #]
# Wireless networks often produce a lot
# of duplicate packets. Set this flag
# to silence duplicate packet warnings.
;mute-replay-warnings
# SSL/TLS parms.
# See the server config file for more
# description. It's best to use
# a separate .crt/.key file pair
# for each client. A single ca
# file can be used for all clients.
#ca ca.crt
#cert client.crt
#key client.key
# Verify server certificate by checking
# that the certicate has the nsCertType
# field set to 'server'. This is an
# important precaution to protect against
# a potential attack discussed here:
# http://openvpn.net/howto.html#mitm
#
# To use this feature, you will need to generate
# your server certificates with the nsCertType
# field set to 'server'. The build-key-server
# script in the easy-rsa folder will do this.
ns-cert-type server
# If a tls-auth key is used on the server
# then every client must also have the key.
;tls-auth ta.key 1
# Select a cryptographic cipher.
# If the cipher option is used on the server
# then you must also specify it here.
cipher AES-128-CBC
auth SHA256
# Enable compression on the VPN link.
# Don't enable this unless it is also
# enabled in the server config file.
comp-lzo
# Set log file verbosity.
verb 3
# Silence repeating messages
;mute 20
# Add key direction
key-direction 1
# script-security 2
# up /etc/openvpn/update-resolv-conf
# down /etc/openvpn/update-resolv-conf
<ca>
-----BEGIN CERTIFICATE-----
...
-----END CERTIFICATE-----
</ca>
<cert>
Certificate:
Data:
Version: 3 (0x2)
Serial Number: 3 (0x3)
Signature Algorithm: sha256WithRSAEncryption
Issuer: C=US, ST=XX, L=MyCity, O=TestArea, OU=Community, CN=TestArea CA/name=server/emailAddress=me@server.com
Validity
Not Before: May 27 02:44:19 2017 GMT
Not After : May 25 02:44:19 2027 GMT
Subject: C=US, ST=XX, L=MyCity, O=TestArea, OU=Community, CN=client1/name=server/emailAddress=me@server.com
Subject Public Key Info:
Public Key Algorithm: rsaEncryption
Public-Key: (2048 bit)
Modulus:
[....]
Exponent: 65537 (0x10001)
X509v3 extensions:
X509v3 Basic Constraints:
CA:FALSE
Netscape Comment:
Easy-RSA Generated Certificate
X509v3 Subject Key Identifier:
...
X509v3 Authority Key Identifier:
...
DirName:/C=US/ST=XX/L=MyCity/O=TestArea/OU=Community/CN=TestArea CA/name=server/emailAddress=me@server.com
serial:[...]
X509v3 Extended Key Usage:
TLS Web Client Authentication
X509v3 Key Usage:
Digital Signature
X509v3 Subject Alternative Name:
DNS:client1
Signature Algorithm: sha256WithRSAEncryption
[....]
-----BEGIN CERTIFICATE-----
...
-----END CERTIFICATE-----
</cert>
<key>
-----BEGIN PRIXXTE KEY-----
.....
-----END PRIXXTE KEY-----
</key>
<tls-auth>
#
# 2048 bit OpenVPN static key
#
-----BEGIN OpenVPN Static key V1-----
.......
-----END OpenVPN Static key V1-----
</tls-auth>
SUCCESSFUL LAN CONNECTIONS # Sample client-side OpenVPN 2.0 config file #
# for connecting to multi-client server. #
# #
# This configuration can be used by multiple #
# clients, however each client should have #
# its own cert and key files. #
# #
# On Windows, you might want to rename this #
# file so it has a .ovpn extension #
##############################################
# Specify that we are a client and that we
# will be pulling certain config file directives
# from the server.
client
# Use the same setting as you are using on
# the server.
# On most systems, the VPN will not function
# unless you partially or fully disable
# the firewall for the TUN/TAP interface.
;dev tap
dev tun
# Windows needs the TAP-Win32 adapter name
# from the Network Connections panel
# if you have more than one. On XP SP2,
# you may need to disable the firewall
# for the TAP adapter.
;dev-node MyTap
# Are we connecting to a TCP or
# UDP server? Use the same setting as
# on the server.
;proto tcp
proto udp
# The hostname/IP and port of the server.
# You can have multiple remote entries
# to load balance between the servers.
remote 10.10.128.16 6354
# Choose a random host from the remote
# list for load-balancing. Otherwise
# try hosts in the order specified.
;remote-random
# Keep trying indefinitely to resolve the
# host name of the OpenVPN server. Very useful
# on machines which are not permanently connected
# to the internet such as laptops.
resolv-retry infinite
# Most clients don't need to bind to
# a specific local port number.
nobind
# Downgrade privileges after initialization (non-Windows only)
user nobody
group nogroup
# Try to preserve some state across restarts.
persist-key
persist-tun
# If you are connecting through an
# HTTP proxy to reach the actual OpenVPN
# server, put the proxy server/IP and
# port number here. See the man page
# if your proxy server requires
# authentication.
;http-proxy-retry # retry on connection failures
;http-proxy [proxy server] [proxy port #]
# Wireless networks often produce a lot
# of duplicate packets. Set this flag
# to silence duplicate packet warnings.
;mute-replay-warnings
# SSL/TLS parms.
# See the server config file for more
# description. It's best to use
# a separate .crt/.key file pair
# for each client. A single ca
# file can be used for all clients.
#ca ca.crt
#cert client.crt
#key client.key
# Verify server certificate by checking
# that the certicate has the nsCertType
# field set to 'server'. This is an
# important precaution to protect against
# a potential attack discussed here:
# http://openvpn.net/howto.html#mitm
#
# To use this feature, you will need to generate
# your server certificates with the nsCertType
# field set to 'server'. The build-key-server
# script in the easy-rsa folder will do this.
ns-cert-type server
# If a tls-auth key is used on the server
# then every client must also have the key.
;tls-auth ta.key 1
# Select a cryptographic cipher.
# If the cipher option is used on the server
# then you must also specify it here.
cipher AES-128-CBC
auth SHA256
# Enable compression on the VPN link.
# Don't enable this unless it is also
# enabled in the server config file.
comp-lzo
# Set log file verbosity.
verb 3
# Silence repeating messages
;mute 20
# Add key direction
key-direction 1
# script-security 2
# up /etc/openvpn/update-resolv-conf
# down /etc/openvpn/update-resolv-conf
<ca>
-----BEGIN CERTIFICATE-----
...
-----END CERTIFICATE-----
</ca>
<cert>
Certificate:
Data:
Version: 3 (0x2)
Serial Number: 3 (0x3)
Signature Algorithm: sha256WithRSAEncryption
Issuer: C=US, ST=XX, L=MyCity, O=TestArea, OU=Community, CN=TestArea CA/name=server/emailAddress=me@server.com
Validity
Not Before: May 27 02:44:19 2017 GMT
Not After : May 25 02:44:19 2027 GMT
Subject: C=US, ST=XX, L=MyCity, O=TestArea, OU=Community, CN=client1/name=server/emailAddress=me@server.com
Subject Public Key Info:
Public Key Algorithm: rsaEncryption
Public-Key: (2048 bit)
Modulus:
[....]
Exponent: 65537 (0x10001)
X509v3 extensions:
X509v3 Basic Constraints:
CA:FALSE
Netscape Comment:
Easy-RSA Generated Certificate
X509v3 Subject Key Identifier:
...
X509v3 Authority Key Identifier:
...
DirName:/C=US/ST=XX/L=MyCity/O=TestArea/OU=Community/CN=TestArea CA/name=server/emailAddress=me@server.com
serial:[...]
X509v3 Extended Key Usage:
TLS Web Client Authentication
X509v3 Key Usage:
Digital Signature
X509v3 Subject Alternative Name:
DNS:client1
Signature Algorithm: sha256WithRSAEncryption
[....]
-----BEGIN CERTIFICATE-----
...
-----END CERTIFICATE-----
</cert>
<key>
-----BEGIN PRIXXTE KEY-----
.....
-----END PRIXXTE KEY-----
</key>
<tls-auth>
#
# 2048 bit OpenVPN static key
#
-----BEGIN OpenVPN Static key V1-----
.......
-----END OpenVPN Static key V1-----
</tls-auth>
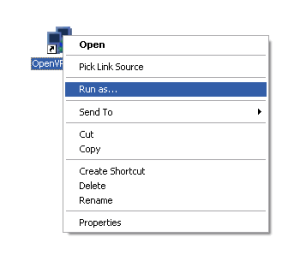
I'm running tcpdump on the external interface (eth1) and once I connect from my laptop MacBook with Yosemite using Tunnelblick 3.7.0 I can see the incoming UDP packet, as well as the response back to the client. Note that while the client MacBook is of course in the private subnet (192.168.24.0/24), the incoming IP is from the router and is a 10.10.128.0/24 range via NAT.
Code: Select all
Obviously I can verify the connection on the client side, but the OpenVPN server output on the server side also shows that everything is working fine:UNSUCCESSFUL INTERNET CLIENT CONNECTIONSNow when I try to connect from the same client from the internet (using my 4G Modem), it can't establish the connection. This is what the Tunnelblick output shows:
Code: Select all
Tunnelblick Not Connecting Video
Obviously, first things first, I confirmed that my external router was correctly setup to forward incoming connection for port 6354 to the VPN server at 10.10.128.16. I did double-check the router configuration and then again ran tcpdump on eth1:The packets are arriving so it's not a router problem. Needless to say that the firewall was my next checkpoint. I am using UFW and I checked both the rules and the status to make sure that connections to port 6354 are allowed from any client:Code: Select all
Finally I checked syslog to see if I could see any problems with OpenVPN or any UFW logs, but neither daemon is logging anything at all.Tunnelblick Connected But Not Working
Tunnelblick Not Connecting Big Sur
I have dug through the configuration files and researched for several days now, but I cannot figure out where the problem could be. Any help would be truly appreciated.Tunnelblick Not Connecting To Internet
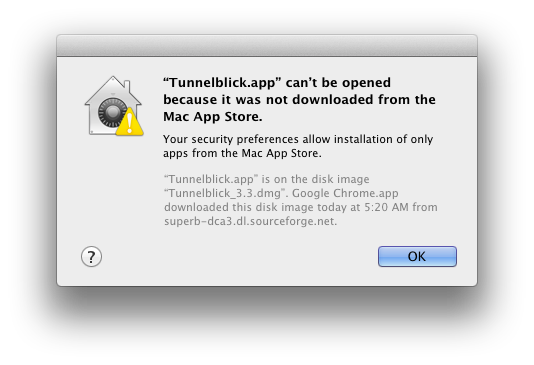
Hi, will like to know how to make tunnelblick connect to my ipcop-VPN.
I have my configuration file. This configuration works with OpenVPN on
Windows fine, but when I place it in the configuration folder of
Tunnelblick I get errors.
My Configration file is saved as .ovpn, and the ca, client, and key
files are zip as pkcs12 eg filename.p12
2010-07-11 13:36:40 *Tunnelblick: OS X 10.6.4; Tunnelblick 3.0 (build
1437); OpenVPN 2.1.1
2010-07-11 13:36:49 *Tunnelblick: Attempting connection with ??_config/
clienttt1-TO-IPCop.ovpn; Set nameserver = 1; monitoring connection
2010-07-11 13:36:49 *Tunnelblick: /Applications/Tunnelblick.app/
Contents/Resources/openvpnstart start ??_config/clienttt1-TO-
IPCop.ovpn 1337 1 0 0 0
2010-07-11 13:36:50 *Tunnelblick: /Applications/Tunnelblick.app/
Contents/Resources/openvpn --management-query-passwords --cd /Users/??/
Library/Application Support/Tunnelblick/Configurations --daemon --
management-hold --management 127.0.0.1 1337 --config /Users/??/Library/
Application Support/Tunnelblick/Configurations/??_config/clienttt1-TO-
IPCop.ovpn --script-security 2 --up '/Applications/Tunnelblick.app/
Contents/Resources/client.up.osx.sh' --down '/Applications/
Tunnelblick.app/Contents/Resources/client.down.osx.sh' --up-restart
2010-07-11 13:36:50 SUCCESS: pid=1910
2010-07-11 13:36:50 SUCCESS: real-time state notification set to ON
2010-07-11 13:36:50 SUCCESS: real-time log notification set to ON
2010-07-11 13:36:50 OpenVPN 2.1.1 i386-apple-darwin10.2.0 [SSL] [LZO2]
[PKCS11] built on Feb 24 2010
2010-07-11 13:36:50 MANAGEMENT: TCP Socket listening on 127.0.0.1:1337
2010-07-11 13:36:50 waiting...
2010-07-11 13:36:50 MANAGEMENT: Client connected from 127.0.0.1:1337
2010-07-11 13:36:50 MANAGEMENT: CMD 'pid'
2010-07-11 13:36:50 MANAGEMENT: CMD 'state on'
2010-07-11 13:36:50 MANAGEMENT: CMD 'log on all'
2010-07-11 13:36:50 END
2010-07-11 13:36:50 MANAGEMENT: CMD 'hold release'
2010-07-11 13:36:50 SUCCESS: hold release succeeded
2010-07-11 13:36:50 NOTE: the current --script-security setting may
allow this configuration to call user-defined scripts
2010-07-11 13:36:50 Error opening file clienttt1.p12 (OpenSSL)
I am using Snow Leopard 10.6.4
Thanks
Node
I have my configuration file. This configuration works with OpenVPN on
Windows fine, but when I place it in the configuration folder of
Tunnelblick I get errors.
My Configration file is saved as .ovpn, and the ca, client, and key
files are zip as pkcs12 eg filename.p12
2010-07-11 13:36:40 *Tunnelblick: OS X 10.6.4; Tunnelblick 3.0 (build
1437); OpenVPN 2.1.1
2010-07-11 13:36:49 *Tunnelblick: Attempting connection with ??_config/
clienttt1-TO-IPCop.ovpn; Set nameserver = 1; monitoring connection
2010-07-11 13:36:49 *Tunnelblick: /Applications/Tunnelblick.app/
Contents/Resources/openvpnstart start ??_config/clienttt1-TO-
IPCop.ovpn 1337 1 0 0 0
2010-07-11 13:36:50 *Tunnelblick: /Applications/Tunnelblick.app/
Contents/Resources/openvpn --management-query-passwords --cd /Users/??/
Library/Application Support/Tunnelblick/Configurations --daemon --
management-hold --management 127.0.0.1 1337 --config /Users/??/Library/
Application Support/Tunnelblick/Configurations/??_config/clienttt1-TO-
IPCop.ovpn --script-security 2 --up '/Applications/Tunnelblick.app/
Contents/Resources/client.up.osx.sh' --down '/Applications/
Tunnelblick.app/Contents/Resources/client.down.osx.sh' --up-restart
2010-07-11 13:36:50 SUCCESS: pid=1910
2010-07-11 13:36:50 SUCCESS: real-time state notification set to ON
2010-07-11 13:36:50 SUCCESS: real-time log notification set to ON
2010-07-11 13:36:50 OpenVPN 2.1.1 i386-apple-darwin10.2.0 [SSL] [LZO2]
[PKCS11] built on Feb 24 2010
2010-07-11 13:36:50 MANAGEMENT: TCP Socket listening on 127.0.0.1:1337
2010-07-11 13:36:50 waiting...
2010-07-11 13:36:50 MANAGEMENT: Client connected from 127.0.0.1:1337
2010-07-11 13:36:50 MANAGEMENT: CMD 'pid'
2010-07-11 13:36:50 MANAGEMENT: CMD 'state on'
2010-07-11 13:36:50 MANAGEMENT: CMD 'log on all'
2010-07-11 13:36:50 END
2010-07-11 13:36:50 MANAGEMENT: CMD 'hold release'
2010-07-11 13:36:50 SUCCESS: hold release succeeded
2010-07-11 13:36:50 NOTE: the current --script-security setting may
allow this configuration to call user-defined scripts
2010-07-11 13:36:50 Error opening file clienttt1.p12 (OpenSSL)
I am using Snow Leopard 10.6.4
Thanks
Node